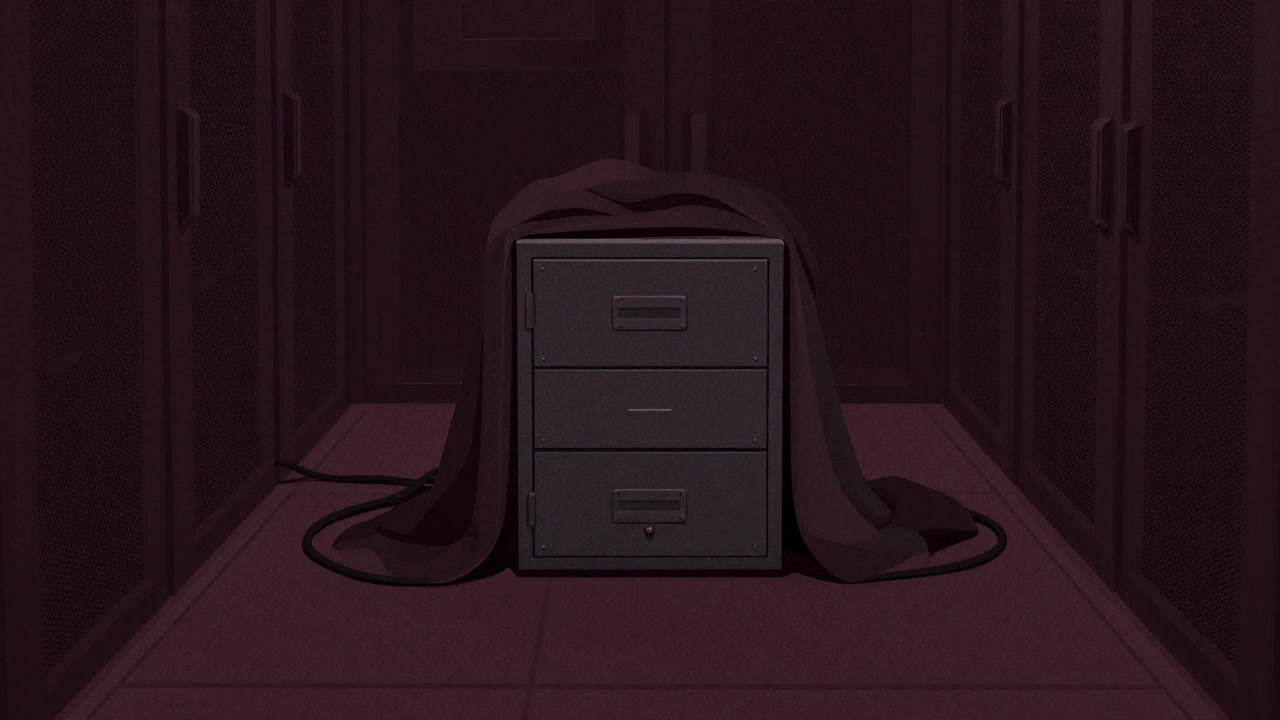
Description
A proclaimed comfort ritual for data slumber that doubles as an excuse generator when key management fails. Encryption at rest quietly shields disks until neglected policies send it into an operational coma. Summoned in audit reports as a showpiece, yet never trusted to actually decrypt anything. It sustains the myth of safety while reducing to a phantom defense that only guards backups. Night after night, administrators feign forgetfulness of passphrases to survive the chaotic midnight reboot festival.
Definitions
- A masquerade ritual to protect quietly sleeping data.
- Where the key is ornamental, the real savior is the excuse ‘At least it is encrypted’.
- An electronic talisman used to fill policy checkboxes.
- A mandatory requirement to thicken documentation rather than improve efficacy.
- A security phantom that flaunts authority only while it slumbers.
- A coat of safety mythology applied to conceal an administrator’s negligence.
- A justification engine for operational costs under the guise of encryption.
- Useless against hacker night raids but a powerful shield against auditors.
- A translucent barrier that is neither as fast nor as robust as proclaimed.
- The rate at which data falls asleep and the rate at which keys are forgotten remain in constant competition.
Examples
- Data safe? It’s encrypted at rest… probably.
- Audit coming? Just write Encryption at rest and hope for the best.
- Performance lagging? Might be it’s busy napping encrypted.
- Where’s the key? What do you mean where, it’s in the administrator’s mind.
- Backup done? Yes, data is snug in its encrypted slumber.
- Data gone? Not gone, just snoozing under encryption.
- Protected against hackers? We’re covered by at rest encryption (if we remember the key).
- Why so slow? Data’s dreaming under its cryptographic blanket.
- Proof of data? It’s wrapped so tightly we can’t peek.
- Can’t access data? Did we forget where we left the key?
- Cloud encrypted at rest too? Yes, but the key is floating in the sky somewhere.
- Production data? Currently in deep slumber.
- Same encryption in dev? Everyone’s sharing the same bed.
- SSD lifespan? Only the keeper of keys knows how long it’ll last.
- Double encryption? Creating data that never wakes up.
- Using Wasabi or S3? Sure, at rest encryption is kindergarten level.
- Decrypt manually? No, we rely on forgetting the passphrase automatically.
- Data corrupted? It just hasn’t woken from encryption dream yet.
- Passphrase management? We write it on infinite sticky notes.
- Disable encryption at rest? Disable? We didn’t know there was such a ritual.
Narratives
- Incident report: encryption at rest is about to be tested by auditors.
- Proclaiming encryption at rest complete with cheer, yet nobody knows the key location.
- Sacrificing performance to raise the encryption flag in policy compliance.
- At midnight backup, key goes missing and chaos ensues.
- Each utterance of encryption at rest etches a new wrinkle on the admin’s brow.
- Opening encrypted data becomes a ritual of admin suffering when keys are forgotten.
- This device of security myth is sliced open by operational mistakes.
- Vendor docs display a shining key but reality offers an illusion on paper.
- Encryption at rest could be data’s final fortress… or so they say.
- Old disks dance with encryption processes, fueling engineers’ all-nighters.
- Encrypt at rest becomes an urban legend to mask the complexity of key management.
- Data bypassing access control is quietly tucked into its encryption bed.
- Clicking Enable encryption at rest becomes a ceremony amid vulnerability fixes.
- Key backups reside in random bug tracker comments, no one dares to touch them.
- Admins wander server corridors at night, searching for sticky notes with the key.
- Encryption at rest is often only invoked as a trump card during migrations.
- The moment backup tapes inherit encryption, a wave of relief sweeps the tech team.
- Data is safest when no one can decrypt because the key is lost.
- Admins bookmark the encryption settings page in preparation for audit questions.
- Ironically, losing the key costs more than having it stolen.
Related Terms
Aliases
- Guardian of Sleeping Keys
- Data Blanket
- Electronic Comforter
- Cryptographic Swaddle
- Policy Warden
- Audit Armor
- Key Forgetter
- Security Veneer
- Silent Shield
- Dozing Encryption
- Silent Security
- Dreamy Gate
- Sleeping Beauty Protector
- Rest Guard
- Key Lost Generator
- Fortress of Illusion
- Sleep Mode Chains
- Performance Thief
- Transparent Bulwark
- Slumber Security
Synonyms
- Dormant Encryption
- Data Quilt
- Policy Cloak
- Talisman on Paper
- Security Mirage
- Audit Offering
- Electronic Plushie
- Key Lost Kingdom
- Void Wall
- Fortress in Dream
- Key Maze
- Secret Slumber
- Sleep Safeguard
- Crypto Mattress
- Static Data Magic
- Security Charm
- Snooze Protection
- Secret Nap
- Backup Cabin
- Hibernate Fort
Use the share button below if you liked it.
It makes me smile, when I see it.