Description
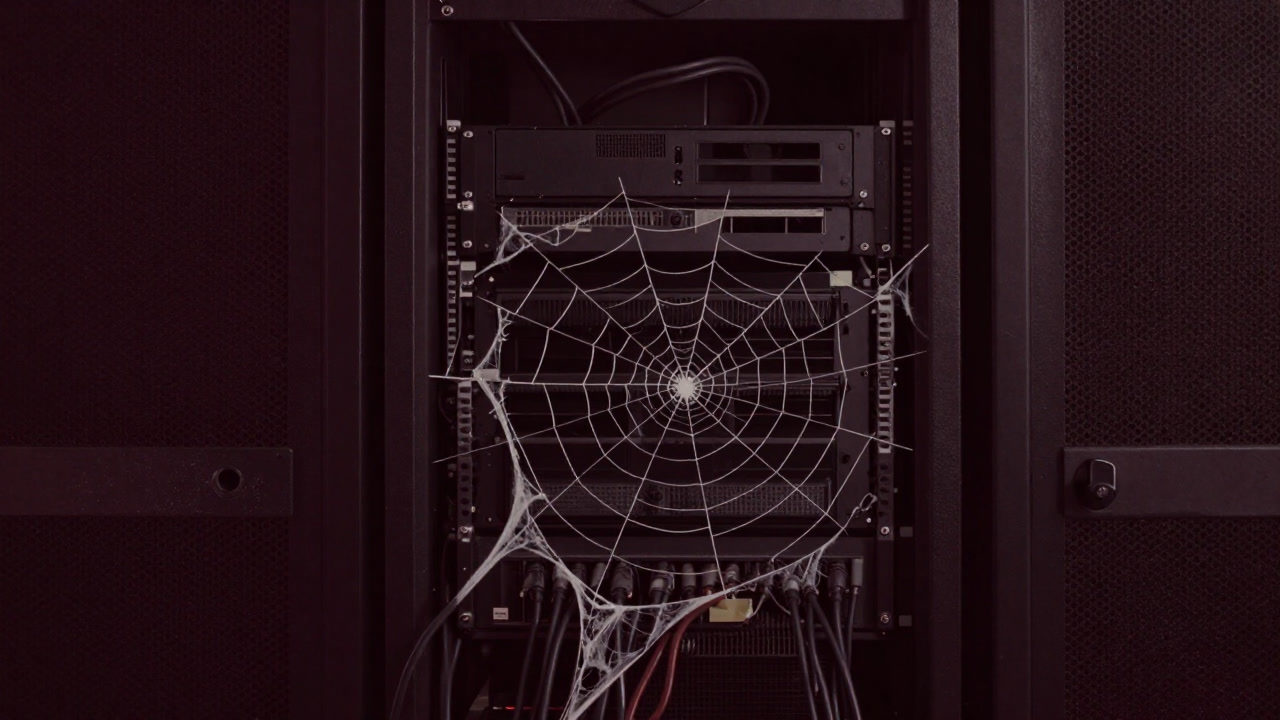
Vulnerability refers to the cracks hidden beneath a system proudly claiming invincibility. Once found, patches rain down as hasty remedies, yet if ignored, send out a banquet invitation to hackers. It is a peculiar gift that offers maximum anxiety and minimal reassurance to those who seek safety.
Definitions
- A system’s weak spot that, when struck, crumbles its protective illusions.
- A dual-faced symbol delivering security officers’ nightmares and hackers’ delights.
- A covert cloak modern software dons in the name of cost-cutting.
- A festival of patches that only matters the moment a flaw is found.
- An invitation banner for attackers to waltz through system defenses.
- The shaky platform sustaining the illusion called safety.
- Seeds of traps mass-produced alongside audit reports.
- The snare where administrators pray for peace yet trip themselves.
- An ideal stage for hackers to display their virtuosity.
- The system’s final unescapable truth unveiled.
Examples
- “A new vulnerability? Here comes the last-minute patch festival again.”
- “This app’s vulnerability generously offers users free anxiety.”
- “Vulnerabilities are mystical when unseen, but become flaming performers once discovered.”
- “Your code hides vulnerabilities too. You might be the first attacker yourself.”
- “The fleeting relief after applying a patch—that’s vulnerability’s true reward.”
Narratives
- A software vulnerability is like a time bomb hidden in a box—its explosion is entirely unpredictable.
- Weekly security alerts are nothing more than invitations penned by vulnerabilities.
- Developers call vulnerabilities ‘bugs’ and create fresh traps each time they fix one.
- Vulnerability management is a ritual of tying shoelaces on the edge of a cliff.
- The vulnerabilities hackers discover slice through corporate pride like a surgeon’s scalpel.
Related Terms
Aliases
- Invisible Mine
- Digital Pitfall
- Anxiety Generator
- Hacker Souvenir
- Invisible Hole
Synonyms
- Security Seed
- Danger Blossom
- Crash Treasury
- Phantom Gap
- Perennial Flamebait
Use the share button below if you liked it.
It makes me smile, when I see it.